Don't Copy From This Blog...
Antivirus Protection Trial is a rogue anti-virus application that reports non-existent infections on your computer. This scareware pretends to scan your computer and find files that are infected, but of course, it's all a lie. It also gives you loads of fake security alerts. The rogue application blocks you from running malware removal tools. Antivirus Protection hijacks web browsers and changes LAN settings and configures your computer to use a proxy server that displays a fake security warning instead of requested website. The rogue program may also randomly open web pages containing explicit/adult content. You are only allowed to go to the Antivirus Protection website to buy their software to remove the threats which do not even exist. Those websites are protection-soft24.com and aviraprotect.com but there might be more.
Antivirus Protection Trial will hijack your web browsers and display fake security warnings. Here's a screenshot of what the fake Internet Explorer warning looks like:

It will also display fake security warnings and alerts every one minute or so. Just like this one which states that your computer is being attacked from a remote machine:

Other fake security alerts:


Here's a screenshot of what the protection-soft24.com (payment page) looks like:

Pretty much the same happens if your computer is infected with another rogue application called Antivirus Monitor. From the HijackThis log we were able to identify the malicious files and changes made to the system. HijackThis log entries related to the Antivirus Protection Trial scareware:
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyServer = http=127.0.0.1:47392
O4 - HKCU\..\Run: [qwhrpdrs] "C:\DOCUME~1\MICHAEL~1\LOCALS~1\Temp\hqwprhsrt\bsqperhder.exe"

As you can see, Antivirus Protection Trial resides in Windows %Temp% folder. It's a randomly named file. Please do not pay for Antivirus Protection Trial. Be advised, if you pay for this phony security software, you will subjected to monetary theft, or in a worst-case example, ID Theft. There is no guarantee that your credit card details aren't going to be sold to other third parties. If you have any further questions, please leave a comment. To remove Antivirus Protection Trial from your computer, please follow the steps in the removal guide below. Good luck and be safe online!
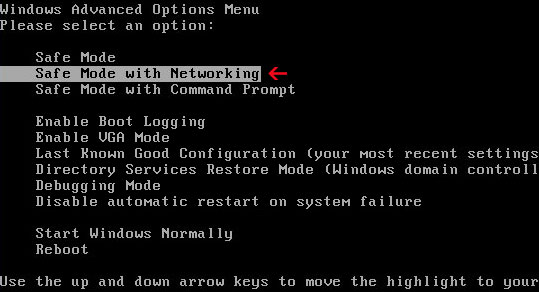
Antivirus Protection Trial removal instructions (in Safe Mode with Networking):
1. Reboot your computer is "Safe Mode with Networking". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Networking" and press Enter key. Login as the same user you were previously logged in with in the normal Windows mode. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm
2. Launch Internet Explorer. In Internet Explorer go to: Tools->Internet Options->Connections tab. Click Lan Settings button and uncheck the checkbox labeled Use a proxy server for your LAN. Click OK.

3. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe, explorer.exe or winlogon.exe. With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
4. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Alternate Antivirus Protection Trial removal instructions (in Normal mode):
1. Download iexplore.exe (NOTE: iexplore.exe file is renamed HijackThis tool from TrendMicro).
Launch the iexplore.exe and click "Do a system scan only" button.
If you can't open iexplore.exe file then download explorer.scr and run it.
2. Search for such entry in the scan results:
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyServer = http=127.0.0.1:47392
O4 - HKCU\..\Run: [SET OF RANDOM CHARACTERS] %Temp%\[SET OF RANDOM CHARACTERS]\[SET OF RANDOM CHARACTERS].exe e.g. bsqperhder.exe
Select all similar entries and click once on the "Fix checked" button. Close HijackThis tool.

OR you can download Process Explorer and end Antivirus Protection Trial process:
- [SET OF RANDOM CHARACTERS].exe, e.g. bsqperhder.exe
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe, explorer.exe or winlogon.exe. With all of these tools, if running Windows 7 or Vista they MUST be run as administrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
4. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Associated Antivirus Protection Trial files and registry values:
Files:
- %Temp%\[SET OF RANDOM CHARACTERS]\
- %Temp%\[SET OF RANDOM CHARACTERS]\[SET OF RANDOM CHARACTERS].exe

%Temp% refers to:
C:\Documents and Settings\[UserName]\Local Settings\Temp (in Windows 2000/XP)
C:\Users\[UserName]\AppData\Local\Temp (in Windows Vista & Windows 7)
Registry values:
- HKEY_CURRENT_USER\Software\[SET OF RANDOM CHARACTERS]
- HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download "RunInvalidSignatures" = '1'
- HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\PhishingFilter "Enabled" = '0'
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "ProxyOverride" = ''
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "ProxyServer" = 'http=127.0.0.1:47392'
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings "ProxyEnable" = '1'
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes" = '.exe'
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
- HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download "CheckExeSignatures" = 'no'

















0 comments:
Post a Comment